Say Hello PCI DSS v4
April 24th, 2024 | By Jscrambler | 5 min read
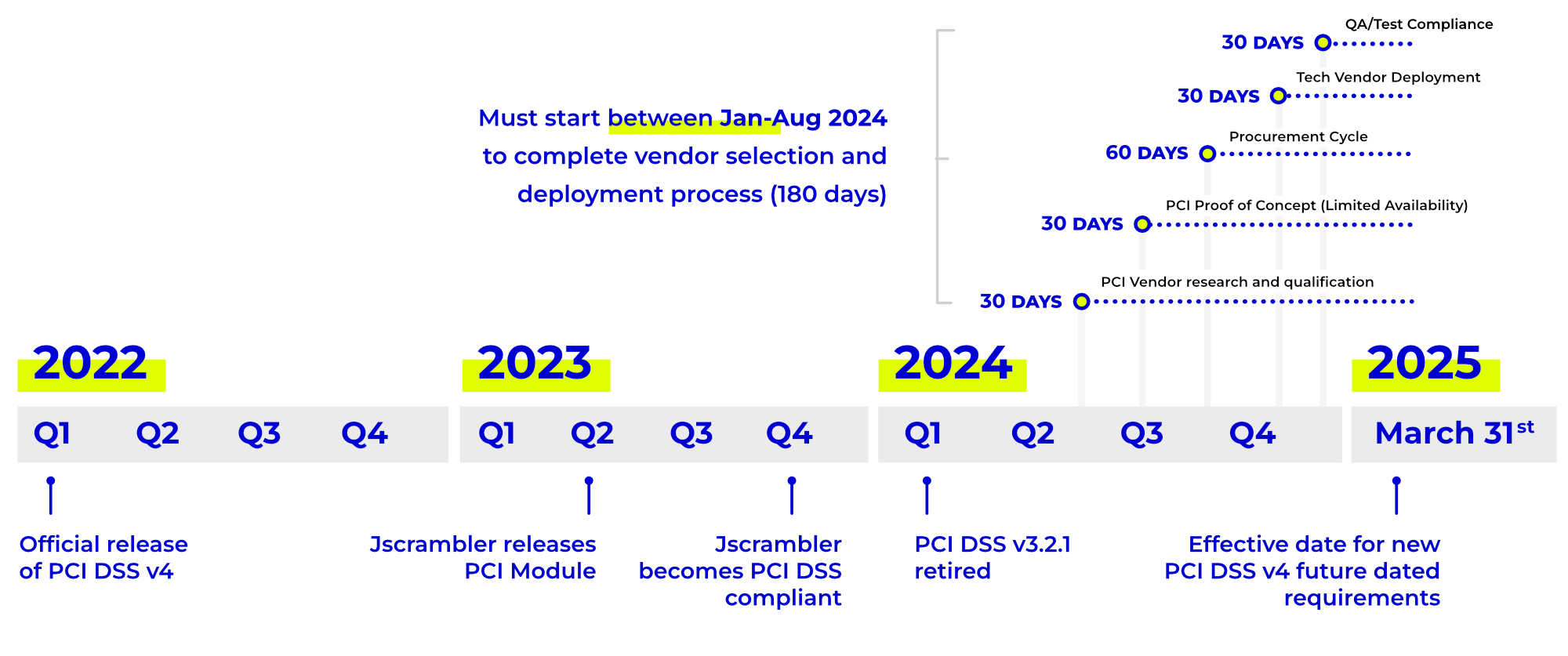
For two years, PCI DSS v4, the latest version of the PCI DSS standard, has been at the forefront of professionals from the payment industry. Version 4 was first released in March 2022, with two years of transition for v3.2.1.
As of March 31, 2024, we’ve officially waved goodbye to this latest iteration and the clock keeps ticking. Like many new requirements in the standard, the ones designed to defeat E-commerce skimming attacks will only become mandatory after April 1, 2025. Until that date, they are described as best practices.
This means they will not be evaluated in a formal PCI DSS assessment until "after March 31, 2025".
Although it seems there is still some time left to worry about it, it’s highly recommended that companies do not delay the implementation of the new security requirements as these E-commerce skimming attacks continue to be increasingly popular today and all e-commerce websites are at risk.
The requirements in PCI DSS v4
The fourth iteration of the standard contains 64 new requirements that organizations seeking compliance must fulfill. Two of these new requirements are focused on the integrity of pages where payment is taken on an e-commerce website and aim to stop e-commerce skimming (Magecart) attacks.
PCI DSS applies to all businesses that accept cards, regardless of how they trade. Let's explore these two requirements:
Requirement 6.4.3 (Preventative)
The first new requirement is designed to minimize the attack surface and manage all JavaScript present on the payment page by requiring an approval process and justification for each script added to the payment page.
It is designed to ensure that all JavaScript included in the payment page is actively managed. Additionally, the requirement wants a way of validating the integrity of a script to be defined to ensure that malicious scripts are not placed on the payment page.
Requirement 11.6.1 (Detective)
The second new requirement aims to detect tampering or unauthorized changes to the payment page, which can indicate a skimming-type attack.
In addition to detecting changes, the requirement demands that an alert be generated when such changes are detected. There is no requirement to block changes or malicious activity, to send an alert.
The business impact of V4
Any organization that wants to accept a transaction with a payment card issued by a PCI SSC participating card brand is required to sign a contract that will contain references to the card brand’s rules, which will specify that:
The organization has to comply with PCI DSS.
The organization must ensure that all of their third-party service providers that can affect the security of cardholder data comply with PCI DSS.
Merchants must gain visibility, risk management, and control over JavaScript before the standard requires it to protect payment card data and guarantee compliance with the new PCI DSS requirements.
Jscrambler’s Solution to Help Achieve PCI DSS v4.0 Compliance
Jscrambler’s Solution allows companies to achieve compliance with the new requirements of PCI DSS v4.0, developed to prevent and detect e-commerce (e.g., Magecart) skimming attacks.
More specifically, we are helping Merchants achieve compliance with requirements 6.4.3 and 11.6.1 of PCI DSS v4.0 and QSAs to validate compliance. Our solution provides merchants with visibility, risk management, and control of all JavaScript running on their websites.
The new requirements mandate that e-commerce businesses maintain a full inventory of every script on their payment page. Businesses are also expected to validate the integrity of every script to ensure that those loaded into the consumer’s browser haven’t been tampered with.
Jscrambler goes one step further than the new requirements and can be configured to automatically block all attempts to skim cardholder data from e-commerce transactions.
To help clear any questions about PCI DSS v4, watch our on-demand webinar - Goodbye PCI DSS v3.2.1, Hello PCI DSS v4. Jscrambler's experts joined Jeremy King, Regional Head of Europe at PCI SSC.
Jscrambler
The leader in client-side Web security. With Jscrambler, JavaScript applications become self-defensive and capable of detecting and blocking client-side attacks like Magecart.
View All ArticlesMust read next
Announcing Partnership with PCI Security Standards Council
Jscrambler and PCI Security Standards Council announced a partnership to protect payment data worldwide.
March 18, 2021 | By Jscrambler | 1 min read
PCI DSS v4 Compliance: The Complete Checklist for Payment Pages
Ensure your e-commerce business meets PCI DSS v4. This complete checklist covers Requirements 6.4.3 and 11.6.1 for securing payment pages against e-skimming and Magecart attacks.
December 23, 2025 | By Nathan Coppinger | 15 min read
Are Non-PCI-Compliant Scripts Putting Your Business at Risk?
Jscrambler has recently achieved attestation against PCI DSS version 4.0. We explain what this means for the security of payment card data on web pages and the risks of non-PCI-compliant scripts.
December 18, 2023 | By Joyrene Thomas | 12 min read